In this article I’d like to look at the difference between Guest Users and Users from another organization directory that I will refer to as Multi-tenant Users. Because as soon as you’d like to give (Azure AD) authenticated guests / users outside of your own organization access to (private) content in WordPress, you will need to understand your options. And there is a lot of potential to get confused and mix up these very different types of accounts.
Guest user
Azure Active Directory allows users from other Azure AD tenants and Microsoft Accounts to be guest users in your Azure AD tenant. These guest users are called External Users. Once an external user is present in your Azure AD tenant, you can permit them access to resources and leverage other Azure AD capabilities like Azure MFA (e.g. requiring them to provide a stronger authentication).
Multi-tenant
When you initially configured the WordPress + Office 365 plugin, you had to register you (WordPress) application in your organization’s Azure Active Directory and created a so-called App registration.
Normally, an App registration lives in (or is “owned by”) a single i.e. your tenant. However, you can change this and enable the App registration for multi-tenancy so that other tenants can “add” and use it as well.
By enabling multi-tenancy for your (WordPress) application by (re-) configuring the corresponding App registration in Azure AD you basically allow users from any other organizational directories or users with a personal Microsoft account to access your content, as soon as they have authenticated successfully.
Guest users versus multi-tenancy: What’s the difference?
The difference between a guest user and a user from another tenant is that the first user actually is registered with your own Azure Active Directory and you can permit / deny them access to resources e.g. to Microsoft Graph, Power BI, Yammer, SharePoint etc, add them to (dynamic) Azure AD security groups and leverage other Azure AD capabilities like Azure MFA whilst the latter is basically does not have an account in your own organization’s directory.
Recommendation
It’s not possible at this point to recommend creating guest users instead of enabling multi-tenancy for your (WordPress) application. What can be said at this point though is that when you enable multi-tenancy you allow
potentially millions of users access to your WordPress website. If your aim is indeed to reach those millions of users without any restriction
e.g. because you’re selling a Software-as-a-service – than enabling multi-tenancy is the way to go.
If your objective is to give your suppliers / partners access to your WordPress based information portal then, however, creating guest users for each one of them seems the better approach. With a small investment you would probably be able to create a simple Guest user provisioning solution using PowerShell, Power Automate and / or PowerApps that will take most of the administrative burden from your shoulders.
Configuration
Perform the following steps to enable multi-tenancy for your WordPress application in combination with the WordPress + Office 365 plugin.
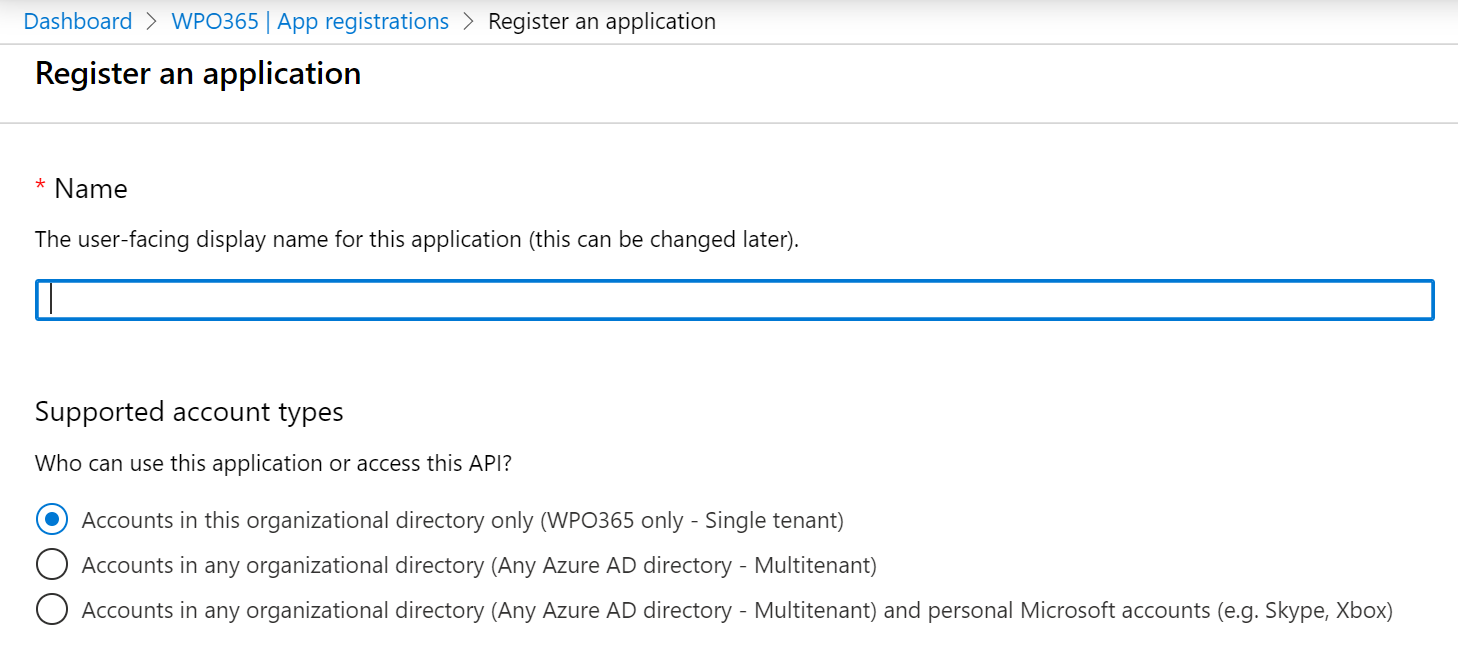
- Navigate to Azure Portal > Azure Active Directory > App registrations.
- Select the App registration that you created for your WordPress application.
- Click Authentication and scroll down to the Supported account types section.
- Make changes as you see appropriate. Please note that if you’d like to add support for personal Microsoft accounts (MSAL) that you register a new application instead.
- Click Save .
- In WordPress navigate to WP Admin > WPO365 > User registration and check the option Allow users from other tenants.
- Go to WP Admin > WPO365 > Single sign-on and update the Domain whitelist if you would like to deny users from domains that are not whitelisted to access your application. Please note that you must also add your own domain(s) (see
Azure Portal > Azure Active Directory > Custom domain names for details). - Test e.g. by launching a new Guest / Incognito browser session, navigate to your WordPress website and sign in with Microsoft using a user from another organizational directory.
Perform the following steps to enable guest users accessing your WordPress application in combination with the WordPress + Office 365 plugin.
- Navigate to Azure Portal > Azure Active Directory > Users and click + New guest user to add a new guest user.
- In WordPress navigate to WP Admin > WPO365 > User registration and ensure that you have not checked the option Allow users from other tenants.
- Test e.g. by launching a new Guest / Incognito browser session, navigate to your WordPress website and sign in with Microsoft using the new guest user.

